Browse articles by topic. From low-level engineering to high-level strategy.
The AI category covers machine learning engineering and practical applications of artificial intelligence. It focuses on understanding how models work and deploying them in real-world contexts:
- Model Architecture: How neural networks are designed, trained, and optimized.
- Topics: Transformers, quantization, inference frameworks, scaling laws.
- Edge AI: Running models on consumer hardware, browsers, and mobile devices.
- Topics:
bitnet.cpp, WebGPU inference, on-device fine-tuning, memory optimization.
- Topics:
An algorithm is a finite sequence of well-defined, computer-implementable instructions, typically to solve a class of problems or to perform a computation. They are the fundamental building blocks of any piece of software.
Key aspects include:
- Efficiency: How well it performs in terms of time and memory ($O(n)$).
- Correctness: Whether it produces the correct output for all valid inputs.
- Design Patterns: Common approaches like divide and conquer, dynamic programming, or greedy algorithms.
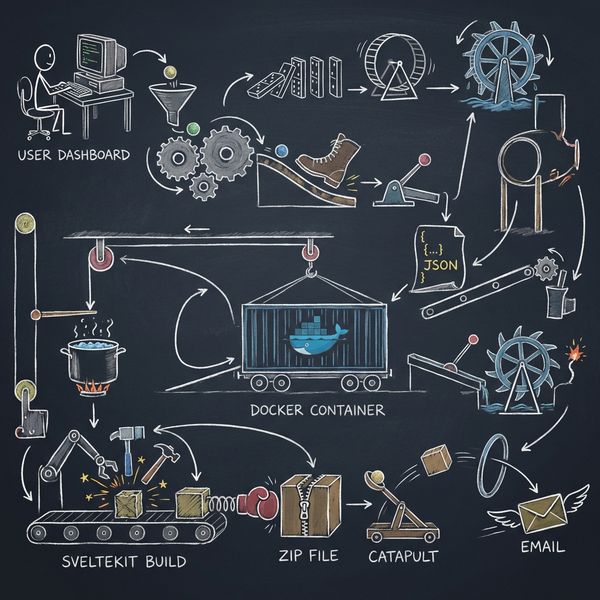
Automation is the application of technology, programs, and robotics to perform tasks that were previously done by humans. In software development and IT, it is crucial for creating efficient and scalable systems.
Key areas include:
- CI/CD Pipelines: Automating the build, test, and deployment of software.
- Infrastructure as Code (IaC): Using code to provision and manage infrastructure.
- Robotic Process Automation (RPA): Automating routine business processes and user interactions.

Run n8n and SearXNG Locally with Docker: Build Your Own No-Code AI Playground
Discover how to set up n8n and SearxNG to build a private AI agent for web searches. You'll have an AI agent that fetches information online without tracking your data. Ideal for those interested in automation and privacy!

Free Online Text to Speech Generator - SpeechStudio.ai
Check out SpeechStudio.ai, a free and powerful text-to-speech tool that provides natural-sounding voices and supports multiple speakers. It's perfect for podcasts, presentations, and creative projects, all without any costs or signups.
Authentication (Auth) is the process of verifying that an individual or system is who they claim to be. It is the first step in any security process and is distinct from authorization (what a user is allowed to do).
Common methods include:
- Something you know: Passwords or PINs.
- Something you have: Security tokens, mobile phones (for OTPs).
- Something you are: Biometrics like fingerprints or facial recognition.
- Multi-Factor Authentication (MFA), which combines two or more of these methods.

GitHub App and OAuth ~ Disjointed flow
Discover how to integrate GitHub App functionality into an existing OAuth-based authentication system. This guide explains how to authenticate as a GitHub App using JWT, retrieve installation IDs, and access repositories associated with the app.
Git is a free and open-source distributed version control system designed to handle everything from small to very large projects with speed and efficiency. Created by Linus Torvalds, it has become the de facto standard for modern software development.
Core concepts include:
- Repositories (
.git): The database tracking all changes. - Commits: Snapshots of your files at a specific point in time.
- Branches: Independent lines of development.
- Merging & Rebasing: Combining changes from different branches.

How to Safely Delete All Local Git Branches
Learn how to quickly and safely remove all local Git branches except the ones you choose (like dev and main) using a simple one-liner command. This guide breaks down each part of the command, provides examples, and tips for a tidier Git workflow.
The Web category covers all aspects of creating and maintaining websites and web applications. It is traditionally split into two main areas, though the lines are increasingly blurred:
- Front-End: The client-side, what the user sees and interacts with in their browser.
- Technologies:
HTML,CSS,JavaScript, and frameworks likeReact,Angular, orVue.
- Technologies:
- Back-End: The server-side, responsible for logic, databases, and authentication.
- Technologies: Languages like
Node.js,Python,PHP,Java, and databases likePostgreSQLorMongoDB.
- Technologies: Languages like
Three.js Static Shadow Baking: One Flag That Saves 20-40% GPU
I posted a Three.js perf thread and got a sharp question back about whether 'baking' was even the right word. The source code said yes and no. Here is what the exchange taught me about `autoUpdate = false`, runtime caching, and a 20-40% GPU win.
Security in the digital realm encompasses all measures taken to protect data, networks, and computer systems from unauthorized access, use, disclosure, disruption, modification, or destruction. It’s a broad field aimed at ensuring confidentiality, integrity, and availability (the “CIA Triad”).
Topics often covered are:
- Vulnerability Assessment: Identifying weaknesses in systems.
- Penetration Testing: Simulating attacks to find exploitable flaws.
- Secure Coding Practices: Writing code that is resilient to common attacks like SQL Injection and XSS.
- Network Security: Protecting the underlying infrastructure with firewalls, VPNs, and monitoring.

Throttling Explained: A Guide to Managing API Request Limits
Learn how to implement a simple and effective throttling system in TypeScript to protect your APIs from overload. This guide covers rate-limiting strategies, IP tracking, and periodic cleanup to manage stale records and optimize performance.